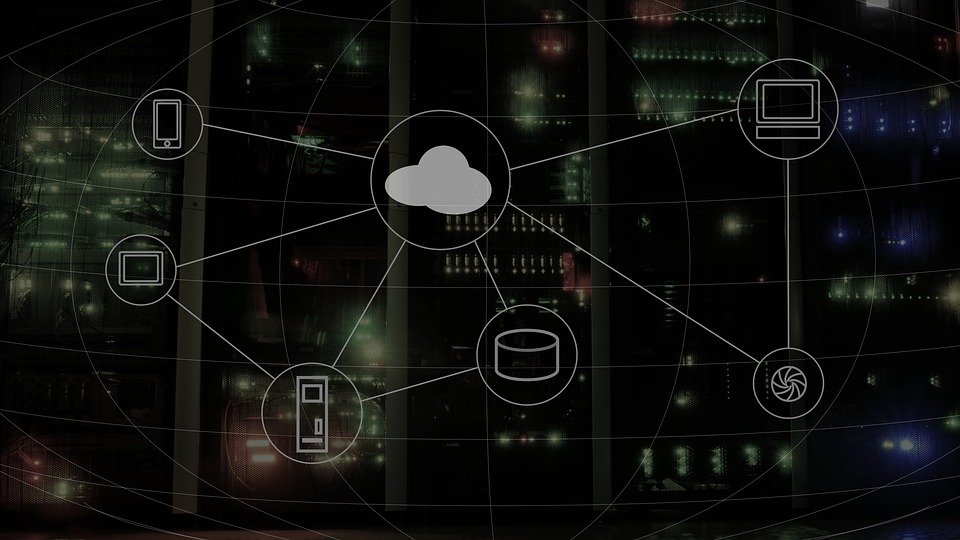
In today’s rapidly evolving digital landscape, connectivity is the linchpin that binds together the diverse facets of our interconnected world. At the heart of this connectivity revolution lays the ubiquitous Application Programming Interface API, a powerful conduit that facilitates seamless communication between disparate systems, platforms, and applications. As businesses and technologies strive for greater integration and efficiency, the exploration of the reach of APIs has become paramount, propelling innovation and collaboration to new heights. APIs serve as the bridges between different software applications, allowing them to communicate, share data, and perform actions seamlessly. This fundamental technology has transcended its role as a mere technical tool, evolving into a critical enabler of digital transformation. Amplifying connectivity through APIs is akin to unlocking the vast potential of a digital ecosystem, enabling businesses to thrive in an interconnected world.
One of the key strengths of APIs is their ability to extend the reach of services and functionalities beyond their native environments. By exposing specific functionalities in a standardized manner, APIs empower developers to leverage existing services to build new applications or integrate seamlessly with other systems. This extensibility has led to the rise of ecosystems where applications from different vendors collaboratively enhance each other’s capabilities, Phishing Detection API documentation fostering innovation and efficiency. Moreover, the reach of APIs extends far beyond the confines of traditional software development. With the advent of Internet of Things IoT and the proliferation of smart devices, APIs play a pivotal role in orchestrating the exchange of information between devices, enabling the creation of intelligent, interconnected ecosystems. This not only enhances user experiences but also opens up new possibilities for automation and data-driven decision-making. The financial sector, for instance, has embraced the reach of APIs to transform the way transactions and financial services are conducted. Open Banking initiatives, powered by APIs, have enabled seamless data sharing between financial institutions, fintech startups, and third-party developers. This has not only enhanced customer experience but has also fostered a more competitive and innovative financial landscape.
The healthcare industry is another realm where the amplification of connectivity through APIs holds immense promise. Interoperability between electronic health record systems, medical devices, and healthcare applications is crucial for delivering efficient and integrated patient care. APIs play a pivotal role in facilitating this interoperability, allowing healthcare providers to access and share critical patient data securely. Despite the immense benefits, the widespread adoption of APIs also brings forth challenges such as security concerns, standardization issues, and the need for effective governance. Addressing these challenges is essential to ensure the continued growth and sustainability of API-driven ecosystems. amplifying connectivity through the exploration of the reach of APIs is a cornerstone of the digital era. APIs empower businesses to transcend traditional boundaries, creating synergies, and driving innovation.